Well, I just arrived home from Seoul, South Korea trip for CodeGate CTF Final.

Our team, CLGT-Meepwn consists of vnsecurity.net’s members and students from my university, University of Information Technology. There are a lot of young guy in Meepwn team. In near future, I wish they could get done our work.
Due to not cheap travelling fee. Organizers has supported 4 of us for transportation and accommodations. So me, k9, tinduong, peter were be sent to Korea.
Day 1, April 30
We had midnight flight from Ho Chi Minh City to Incheon International Airport, and arrived there at 7:00 AM, then took the train to our hotel in Gangnam. It was near to COEX Mall (where the competition is placed). That night, We just walked around and eat, drink something nearby.

Day 2, May 1
This is the 3rd time I come Korea. Every time, when wake up, I always feel fresh although I often don’t sleep enough when I’m not in Vietnam :p. Then we took a round through COEX, buy some stuff. We even watched Captain America: Civil War in midnight, when the train MRT was closed, then we had to walk home, and we went sleep at 5:00 AM next day.



Day 3, May 2
11:00 AM, we woke up and went to COEX.
2:00 PM competition started. There were like 5-6 tasks in the beginning which are in various categories such as: web, reverse, misc. Later, some pwnable tasks were released, two of them are interesting (hackerlife, exploitshop). Most of web tasks are likely related to SQL Injection, PHP Object Injection, Flask tricks, etc. In my opinion, it’s not quite hard. Each one of them is solved by approximately 6-8 teams. A bit later, k9 successfully finished misc task about radio signal processing, tinduong also solved Golang binary. We were getting better and more inspiration. During the contest, me-k9-tinduong concentrated on web/reversing/misc tasks. I also helped Peter to solve pwnable tasks. hackerlife was about Uninitialized value, we did determine this bug, but we could not complete it. When the game was running out of time, we decided to focus on exploitshop. This one was about SQL-Injection indeed. You need to trigger the SQLi bug and lead it to buffer-overflow (binary is compiled without SSP). These pwnable tasks were solved by about 4~6 teams. But we didn’t make it happens :(.

When 15 minutes before the game ended, LC-BC (Russian team) got one more task and defeated PPP, became 1st. I thought “OMG, this year will end like this again ?”. Cause you know, last year, 0ops (China team) in last 15 minutes, they beat PPP and finished as a winner.
And the final scoreboard is showed up like this.

But…the drama began. The organizers announced that LC-BC is disqualified due to getting help from remote players, which is considered cheating, breaking the rules. And PPP became a winner !!!
0daysober, 217 are following up as runner-up and third place.
The challenges will be uploaded by orangizers soon I think.
Then we got back to our room, got some sleep and went to Network(beer) session. In this session, I hangout with few old friends who I met them before. It was really really fun to me. At the first time I was in Korea, I was a little shy and feel no confidence to talk to everybody. We talked a lot of things about Korea, Viet Nam and we hope that one day, we would meet each other again !! (y).
Day 4, May 3
We were heading back to Ho Chi Minh. This trip is awesome, i’ve been learning many things. After every journey, I feel more motivated. Those guys, competitors, friends are inspiration to me.
Side Story (PHP Bug Bounty)
As I did tweet before
in one month and a half, i’ve found and reported 08 bugs to PHP.
they patched and fixed all of them so far. it was interesting.— Luat Nguyen (@manhluat93) March 4, 2016
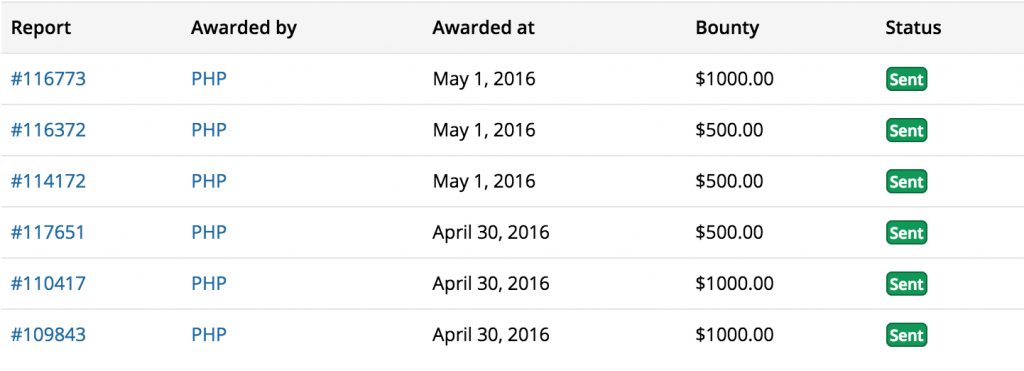
Few days ago, I got a notice that they (PHP & Internet bug bounty on hackerone.com) accepted my bugs, and considered to be eligible for bug bounty.
Details of these bug are described below. I found these bugs by auditing and fuzzing as well, and I realize that CTF helped me to improve my skills a lot. Auditing is what I learned from Exploiting challenges.
The following are security bugs which I’ve reported:
- https://bugs.php.net/bug.php?id=71587 (CVE-2016-3141)
- https://bugs.php.net/bug.php?id=71610 (CVE-2016-3185)
- https://bugs.php.net/bug.php?id=71498 (CVE-2016-3142)
- https://bugs.php.net/bug.php?id=71637 (CVE-2016-4344, CVE-2016-4345, CVE-2016-4346)
- https://bugs.php.net/bug.php?id=71354 (CVE-2016-4342)
- https://bugs.php.net/bug.php?id=71331 (CVE-2016-4343)
I know, this bug bounty is not much “money” than other guys :p. But it’s pretty meaningful to me :).


[…] Final Scoreboard as captured by manhluat (l4w) […]
chú giỏi đó , dám nghĩ dám làm, dám đi con đường gần như tiên phong lĩnh vực cntt ở vn :)) , good job guy